Context
Security operations are relentless. Analysts and IT administrators are bombarded with hundreds of alerts daily across fragmented dashboards, from network performance tools to threat detection systems and compliance monitors. Each alert demands attention, triage, and a response that often follows a well-worn path: check the logs, review policies, apply a fix, run tests, confirm resolution.
This repetitive, high-stakes work doesn't just consume time. It consumes people. Organizations routinely dedicate entire roles to watching dashboards and manually working through these cycles, day after day.
At Cisco, we saw an opportunity to change that.
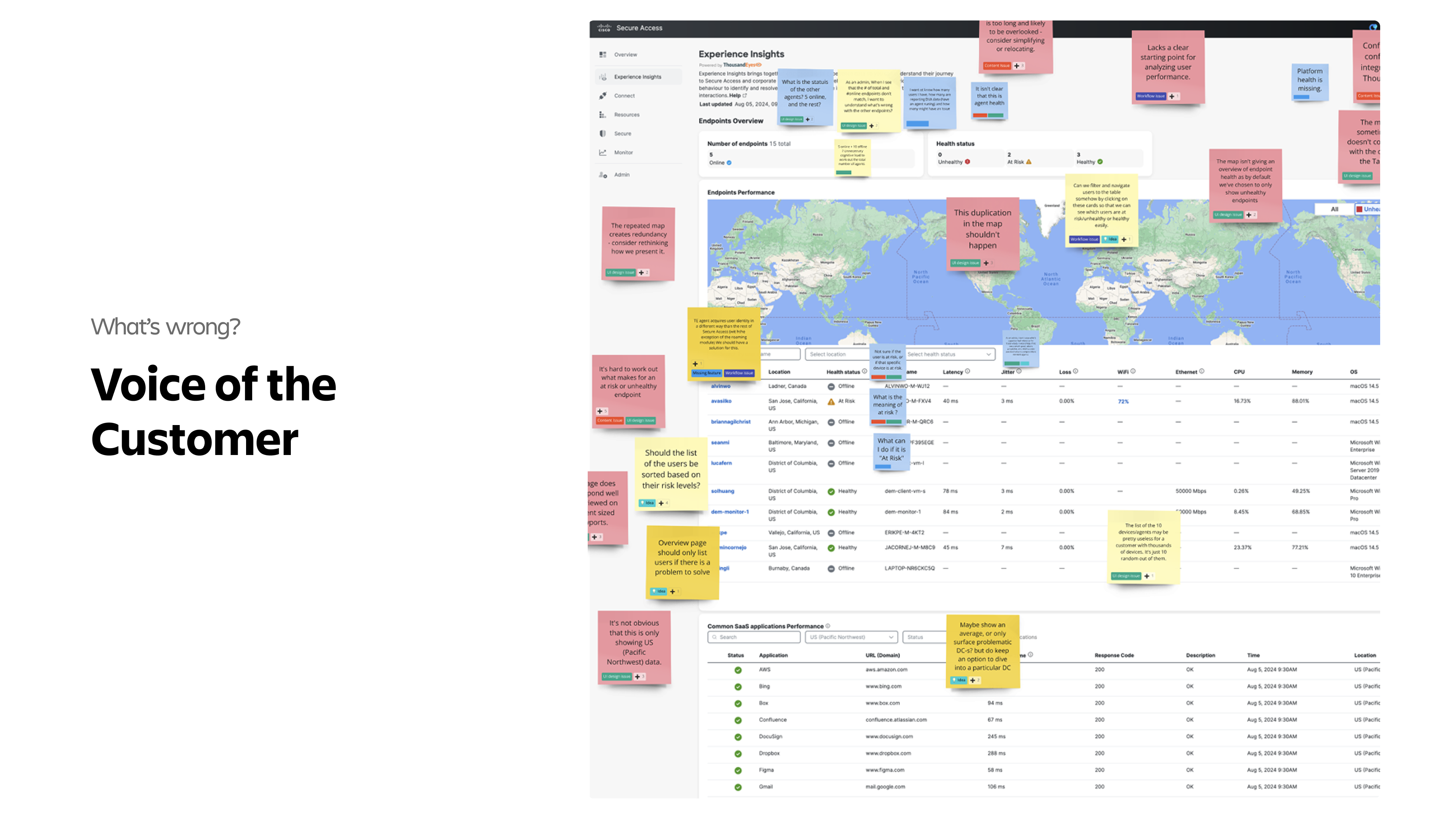
Challenge
The core tension was clear but nuanced:
The problem wasn't that admins didn't know what to do. The problem was how long it took them to do it, repeatedly.
Security workflows, while predictable in structure, require pulling context from multiple sources like Secure Access, ThousandEyes, firewall logs, and compliance reports, and stitching that picture together manually before any action can be taken. This meant:
- Alert fatigue from monitoring too many dashboards simultaneously
- High cognitive load in interpreting fragmented data before taking action
- Slow time-to-resolution due to repetitive, manual troubleshooting steps
- Bottlenecked teams where skilled analysts spent the majority of their time on routine triage rather than high-value investigations
The obvious answer would be full automation. Let AI handle it. But security is a deeply sensitive domain. Teams are not yet ready to hand full autonomy to systems to act on their behalf without oversight. Any solution that bypassed human judgment would face immediate resistance and legitimate trust concerns.

So the challenge became:
How do we dramatically reduce the time and effort of routine security workflows without removing the human from the equation?
Approach
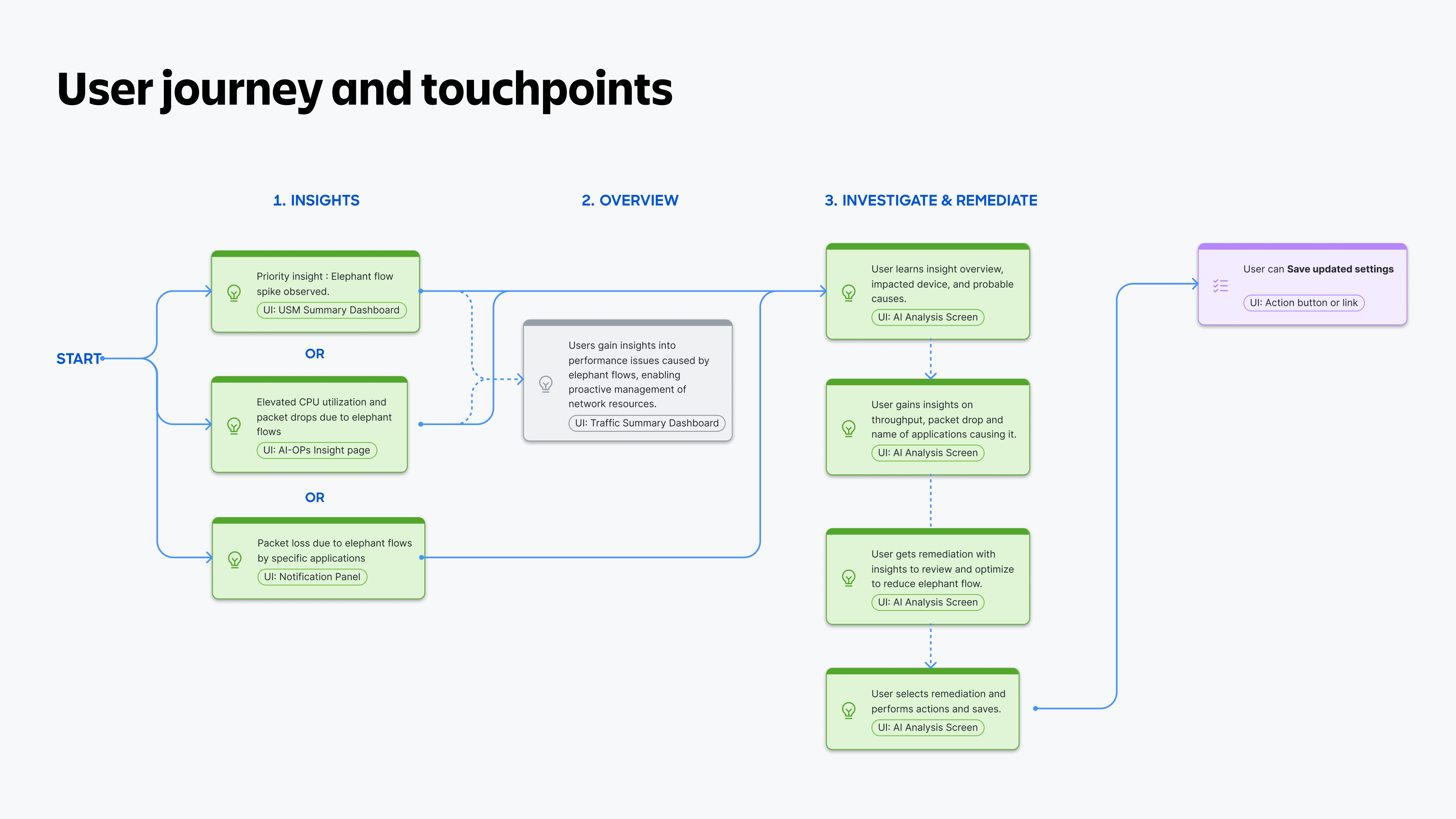
We started by deeply studying how security analysts actually work. The insight that shaped everything was this: the paths are repetitive, but the decisions still need a human hand.
Analysts weren't reinventing the wheel each time an anomaly was detected or a compliance gap surfaced. They were following mental playbooks they'd built over years. Our job was to externalize and operationalize those mental models into guided, AI-assisted flows.
Key design principles we established:
- Synthesis over noise: Reduce the number of things an admin needs to look at by surfacing only what's most relevant to them, personalized to their role and context. No more jumping between tools.
- Assisted, not autonomous: AI prepares the path, the human walks it. Every action is suggested, not automatic.
- Role-aware intelligence: Insights and playbook triggers should reflect what a Security Analyst specifically needs, not a generic alert feed.
- Trust through transparency: Show the admin why something was flagged and what the recommended steps are before they commit to any action.
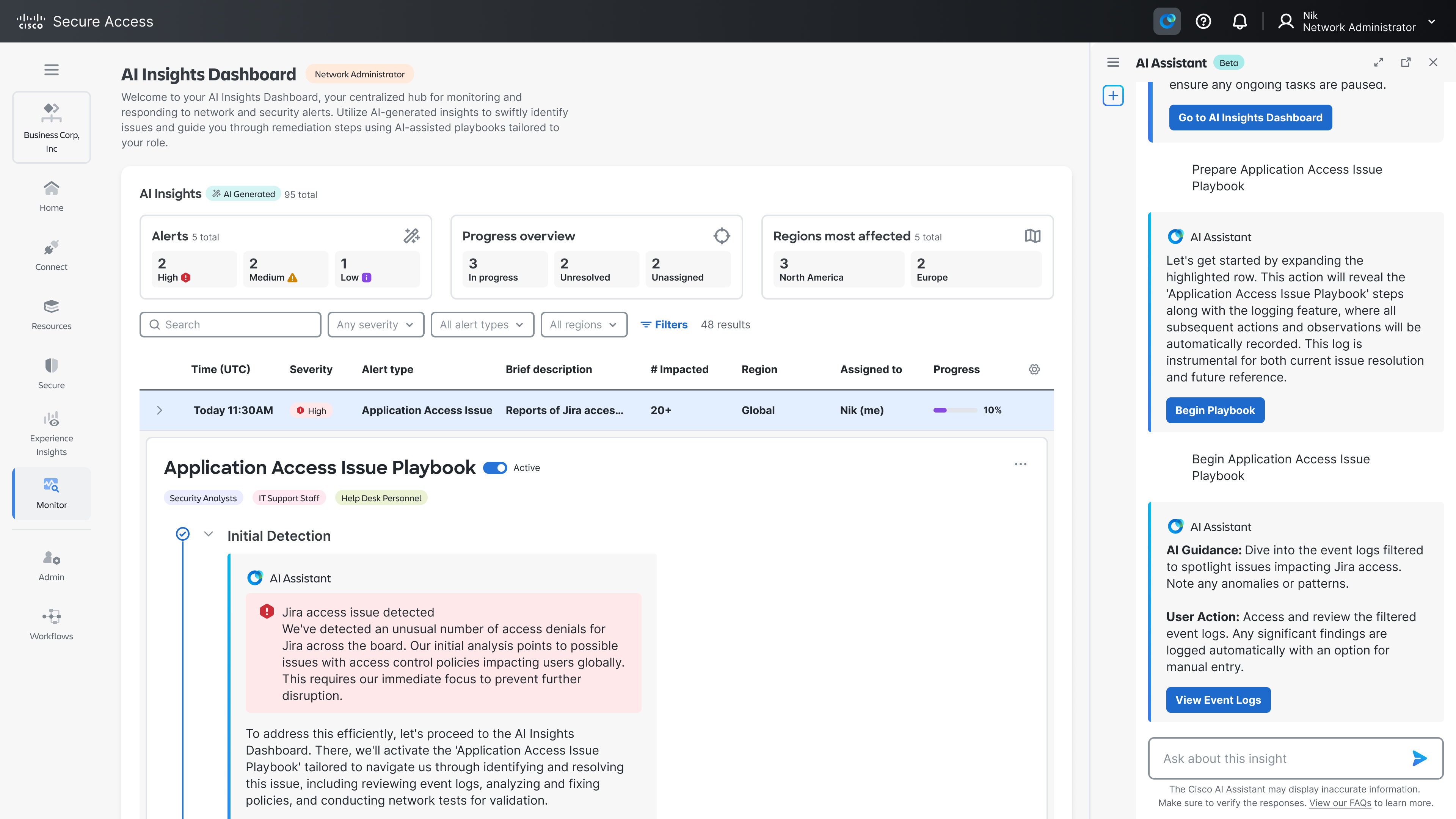
We designed the Insight Dashboard (Security Analyst Edition) as the entry point, a personalized AI Action Center that synthesizes signals from across Cisco's security suite into a curated, prioritized feed of what needs attention right now.
From each insight card, admins can launch a Playbook, a structured, AI-guided workflow that walks them through the exact steps needed to investigate and resolve that specific issue, pulling in relevant data automatically at each step.
Solution
The solution manifests in two interconnected layers:
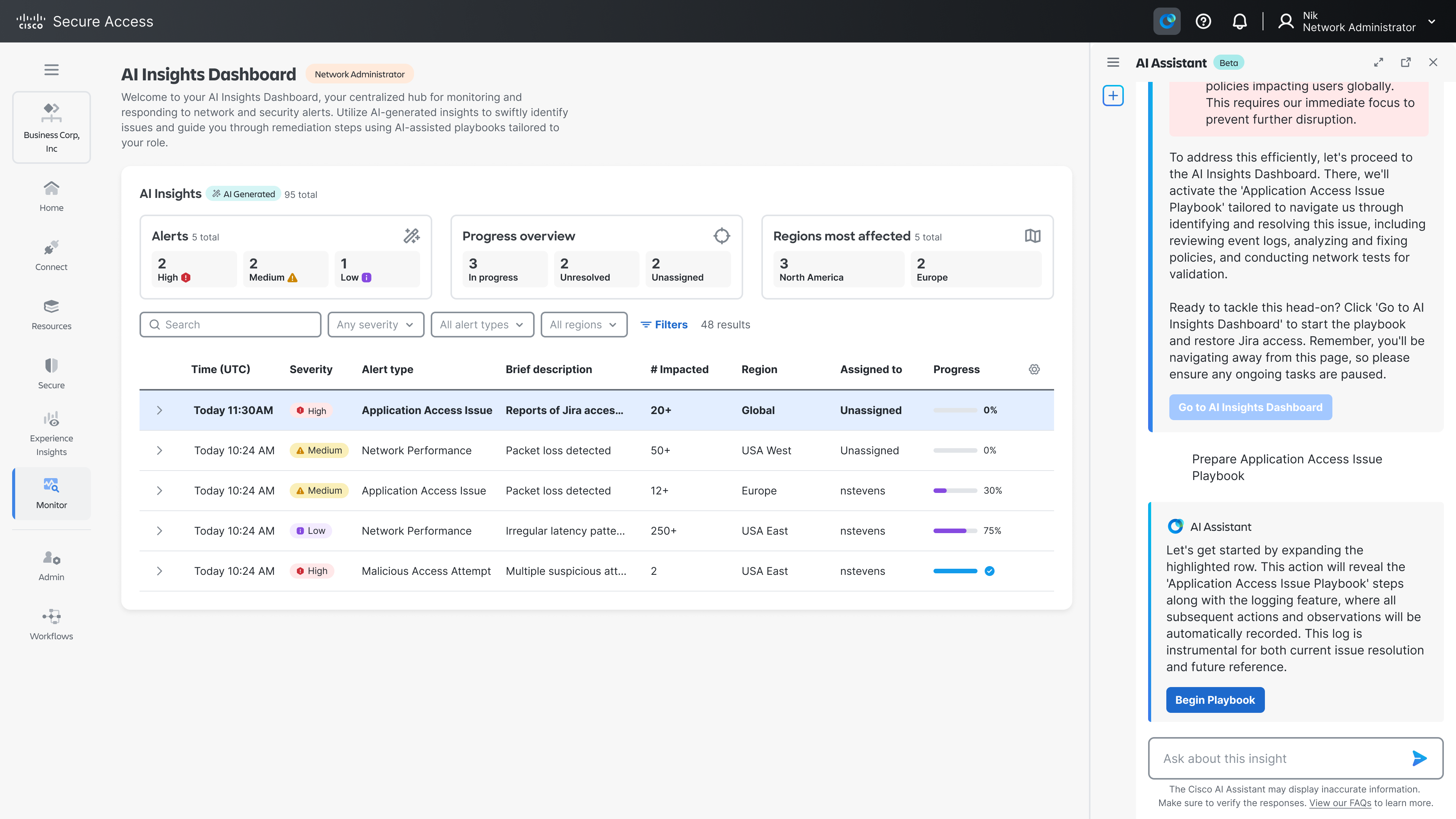
1. The Insight Dashboard
A role-specific, AI-curated view that replaces the need to monitor multiple tools simultaneously. Rather than asking an admin to visit Secure Access, ThousandEyes, and compliance tools separately, the dashboard aggregates and prioritizes:
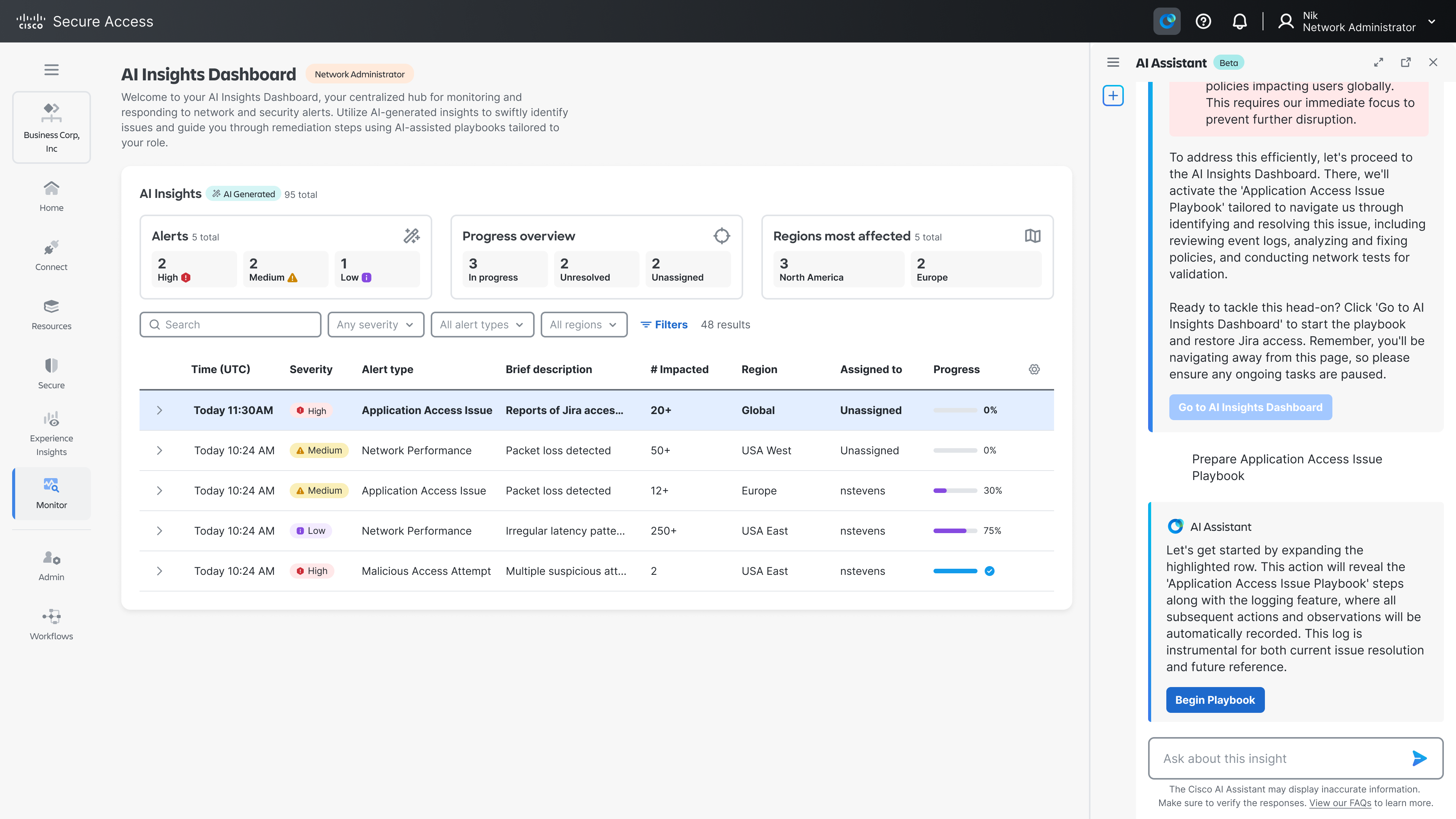
- Threat Landscape Overview: New security alerts since last login, with a ready-to-go response playbook
- Anomaly Detection: Unusual login patterns flagged from specific departments, pointing to potential credential misuse
- Network Performance Alerts: ThousandEyes-detected performance drops in specific regions, tied directly to impacted users
- Risk Assessment Updates: Probing attempt trends on web servers, with firewall rules already auto-adjusted for review
- Compliance Checks: Endpoint compliance status with discrepancies highlighted for immediate resolution
Each card surfaces only what's actionable, includes a plain-language explanation of the issue, and offers a direct pathway to act, removing the need to hunt for context.
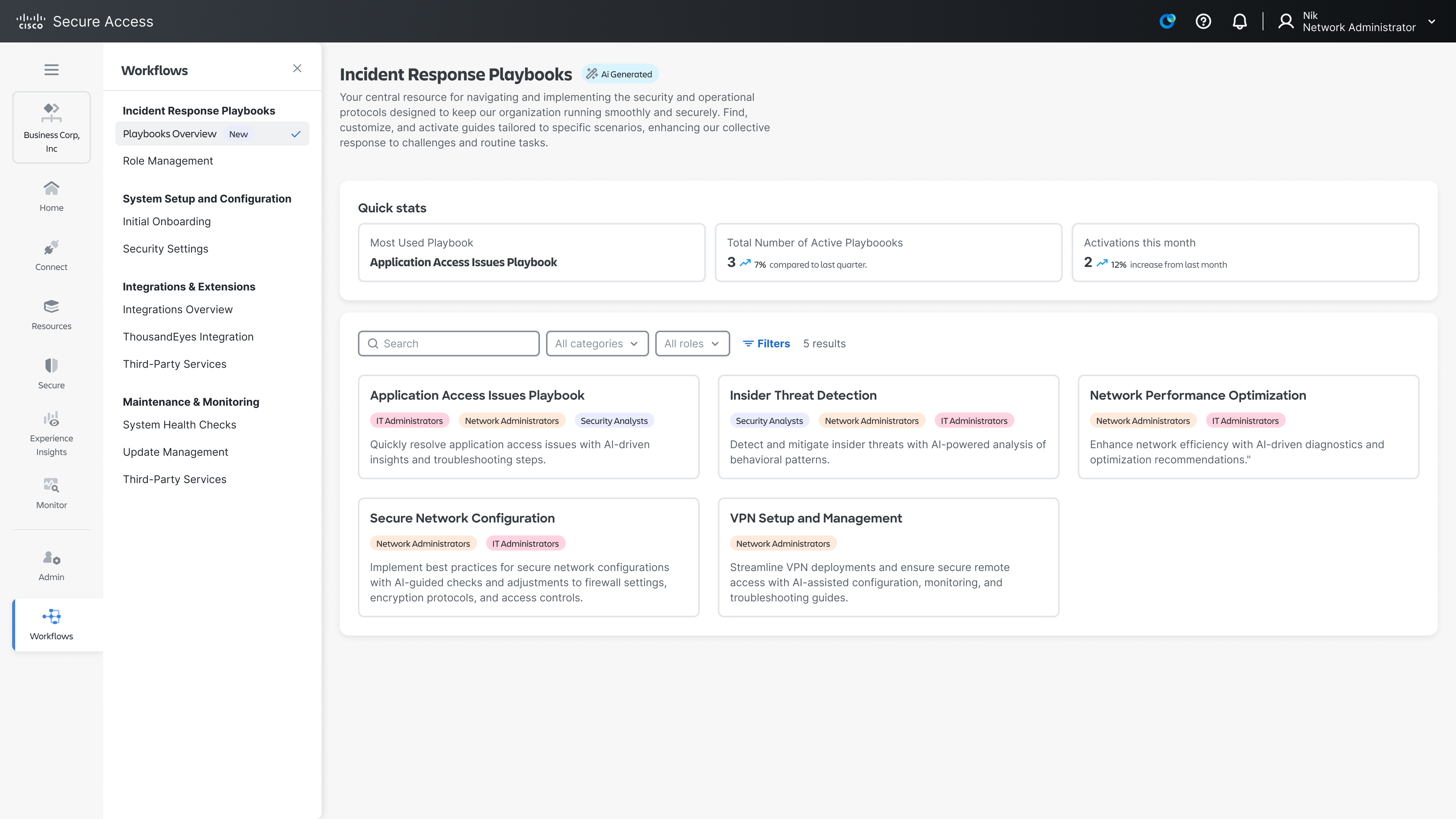
2. Playbooks
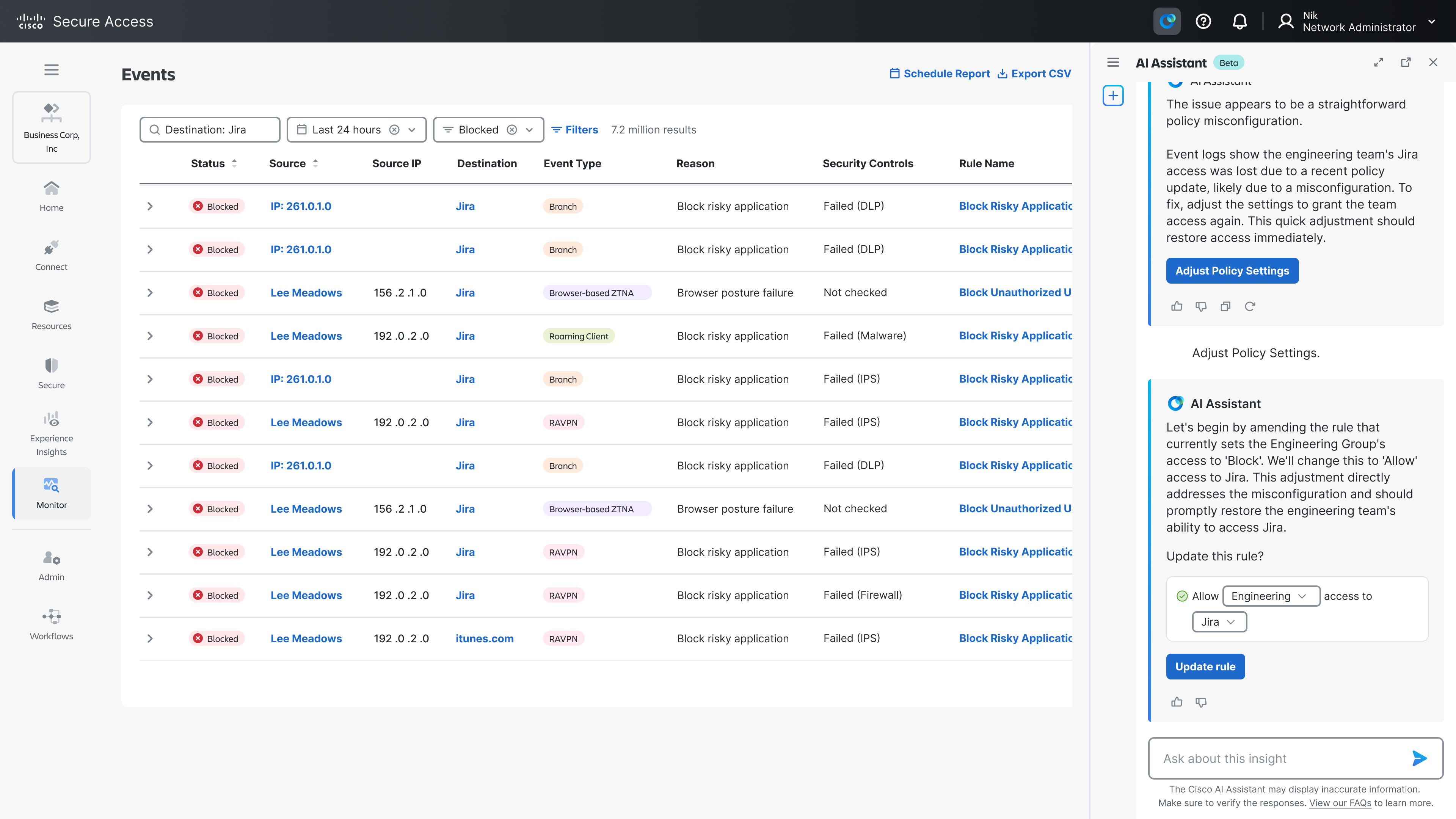
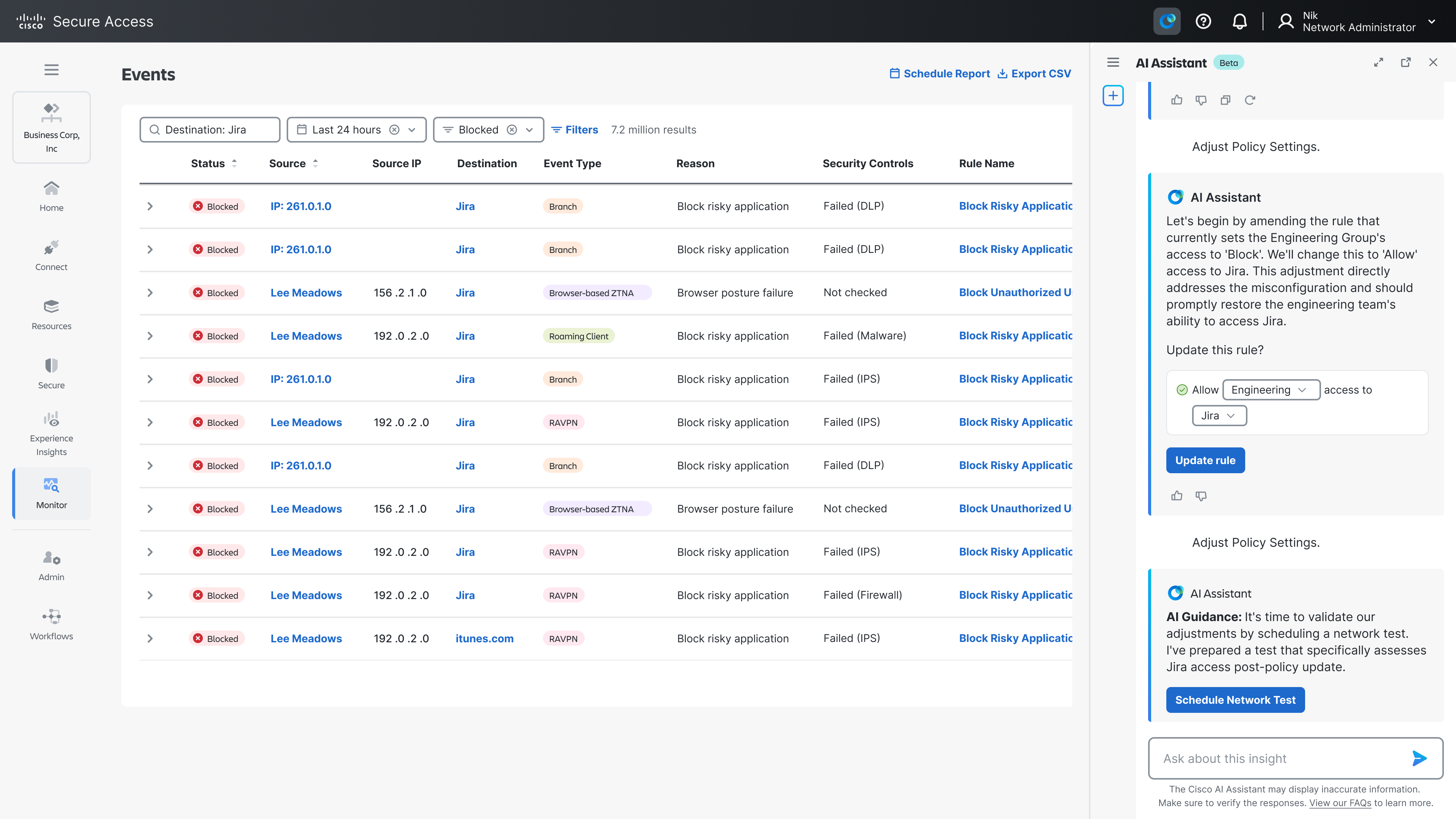
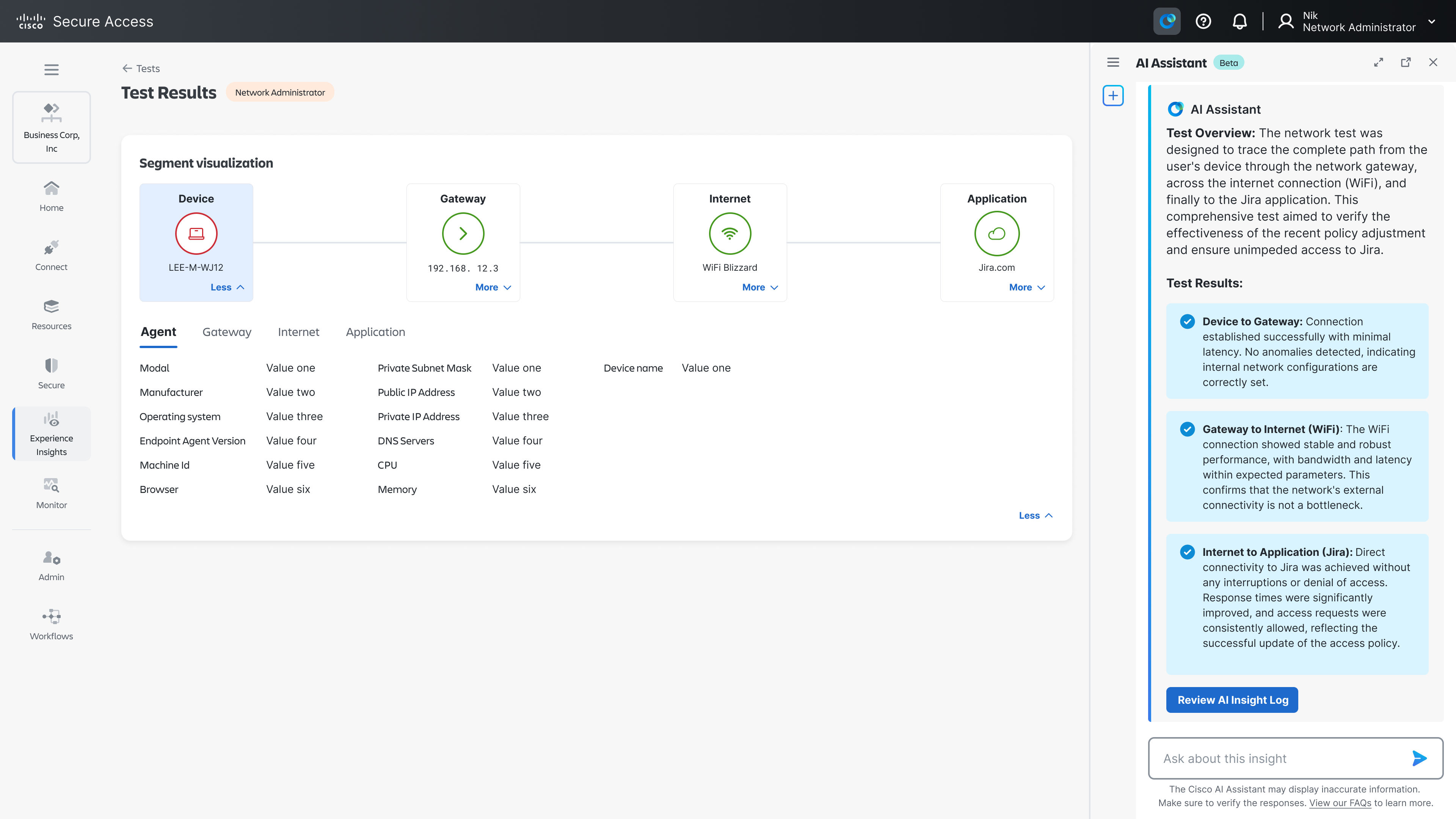
Playbooks are the engine behind each insight card. When an admin clicks "Investigate Login Anomaly" or "Diagnose Performance Drop," they enter a guided, AI-assisted workflow that:
- Automatically pulls relevant logs, policies, and diagnostic data
- Steps the admin through the investigation in a logical sequence
- Highlights decision points where human judgment is required
- Suggests resolutions with clear rationale
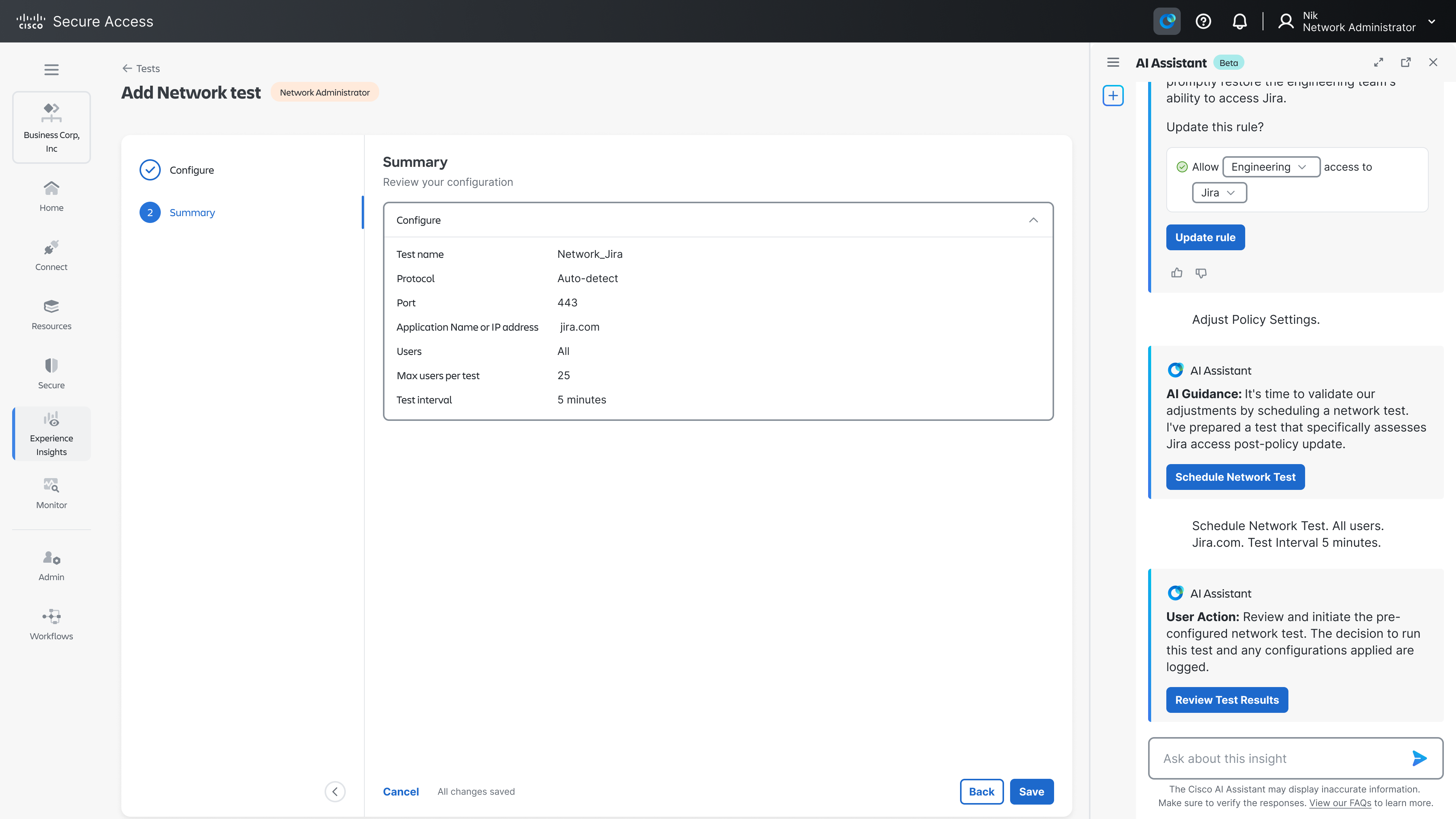
- Confirms outcomes before closing the loop
Playbooks are built for specific use cases, each one encoding the institutional knowledge of experienced analysts into a repeatable, AI-augmented process. Admins aren't following a rigid script and retain full control, but the heavy lifting of data gathering and context-building is done for them.
Let's review how it works in a real-world flow;
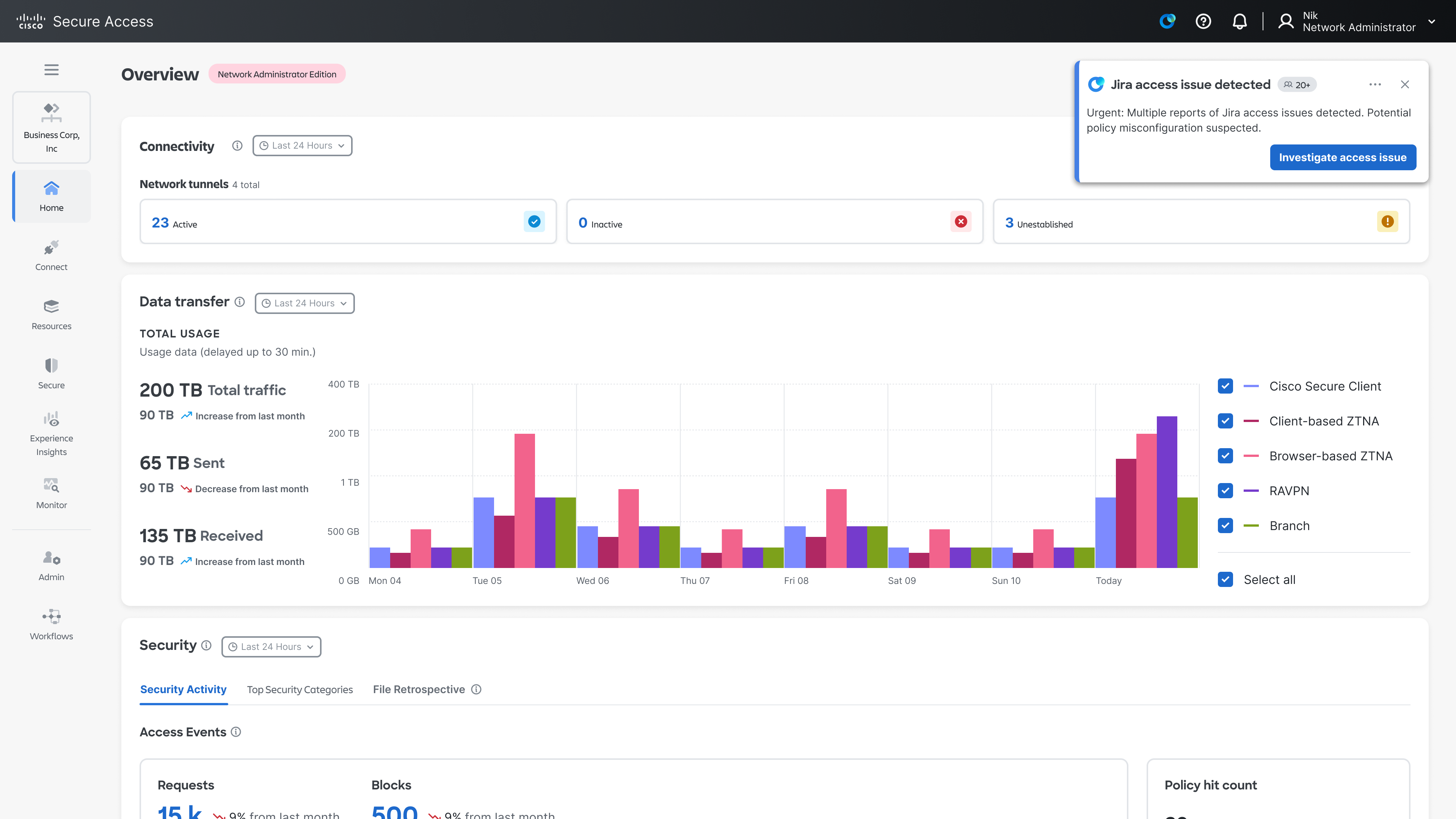
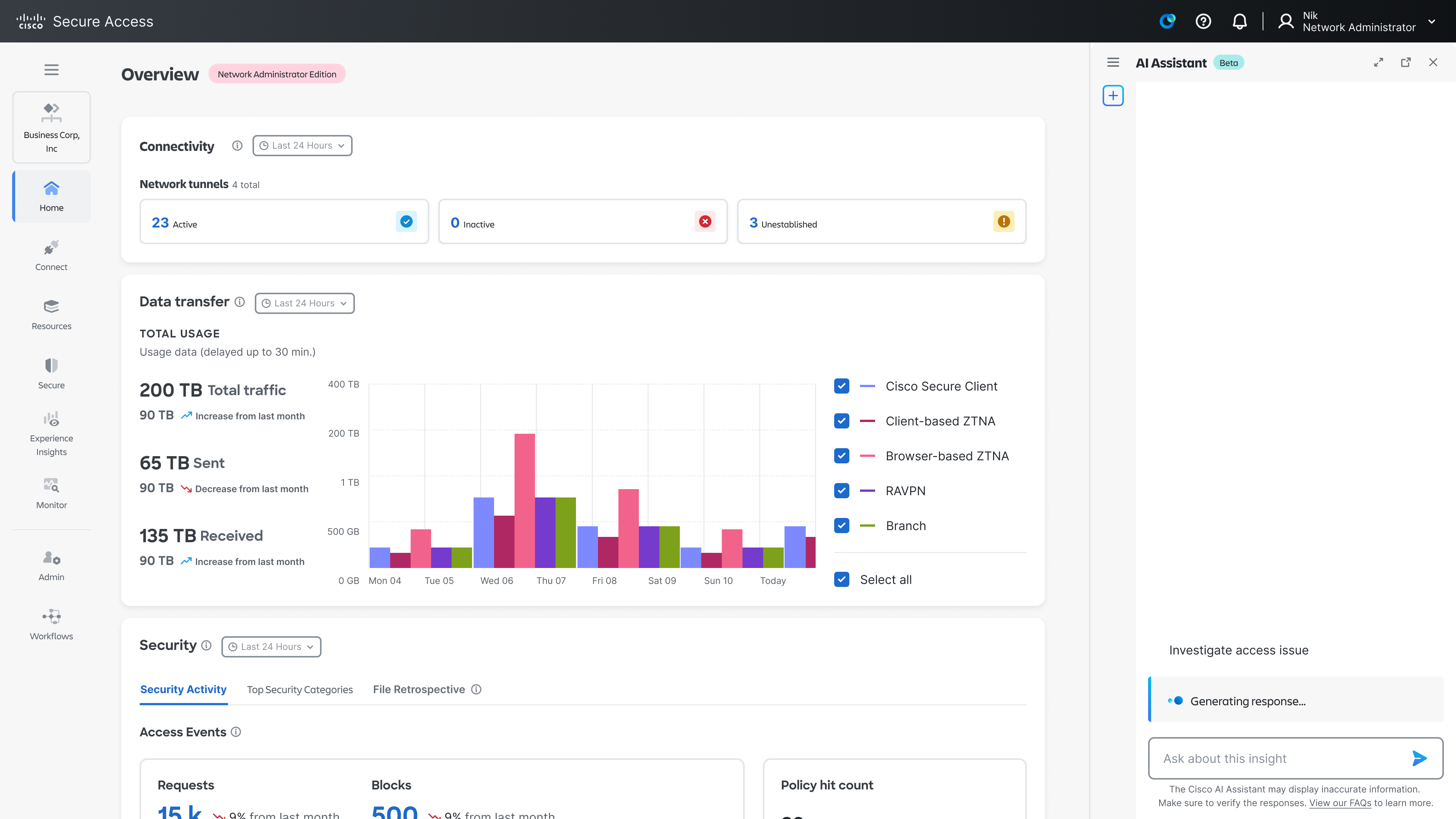
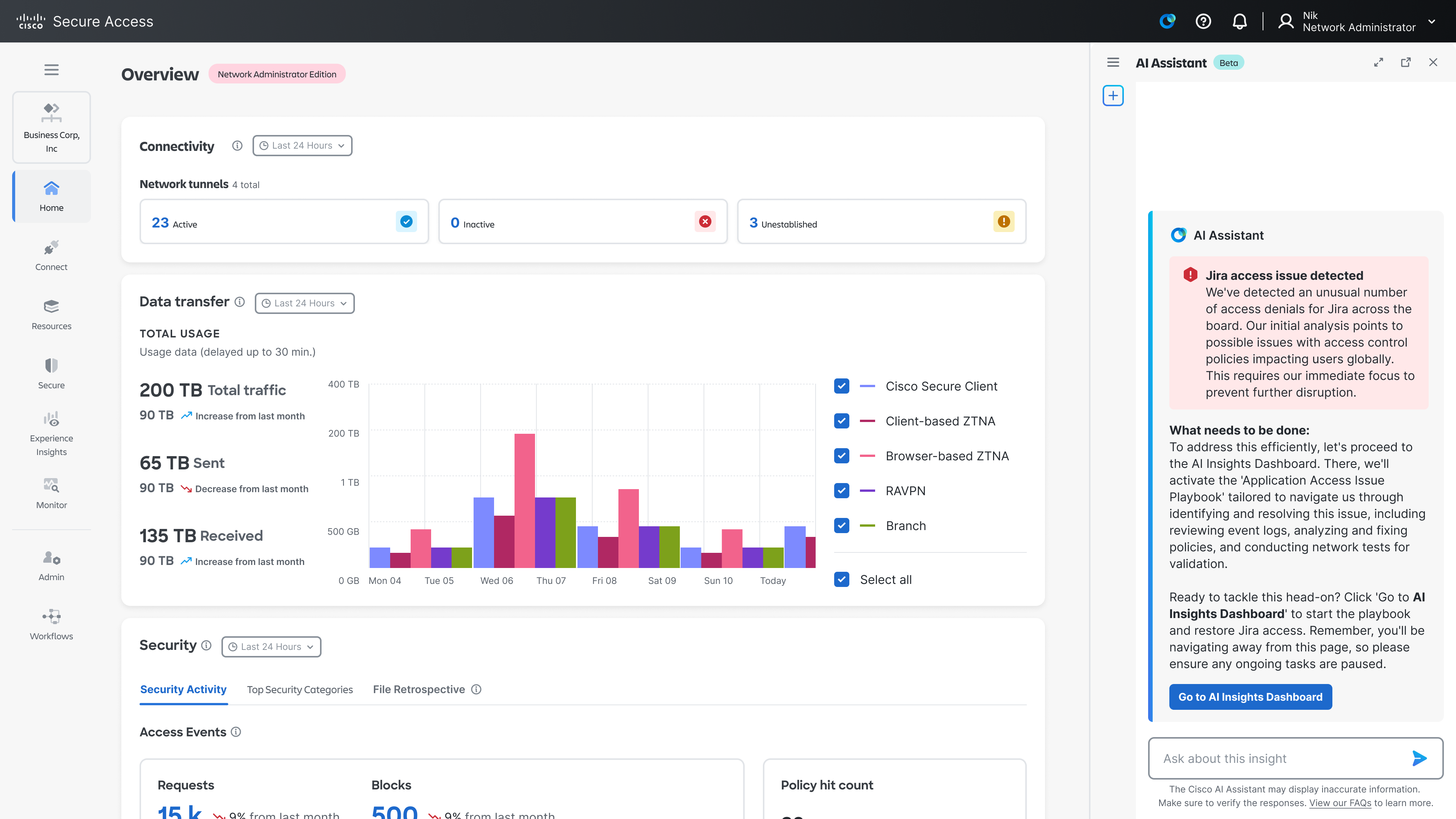
AI Insights Dashboard
Policy Engine in works
Test the results
Outcome
The results were significant:
- Time-to-resolution reduced by approximately 1/3 compared to traditional manual workflows
- Alert fatigue reduced by consolidating multi-tool monitoring into a single, prioritized Insight Dashboard
- Faster, more confident decisions as admins spend less time gathering context and more time making judgment calls
- Trust preserved as the human-in-the-loop model was well received by security teams who weren't ready to cede control to fully autonomous systems
- Scalability unlocked as teams can handle a higher volume of alerts without proportionally increasing headcount
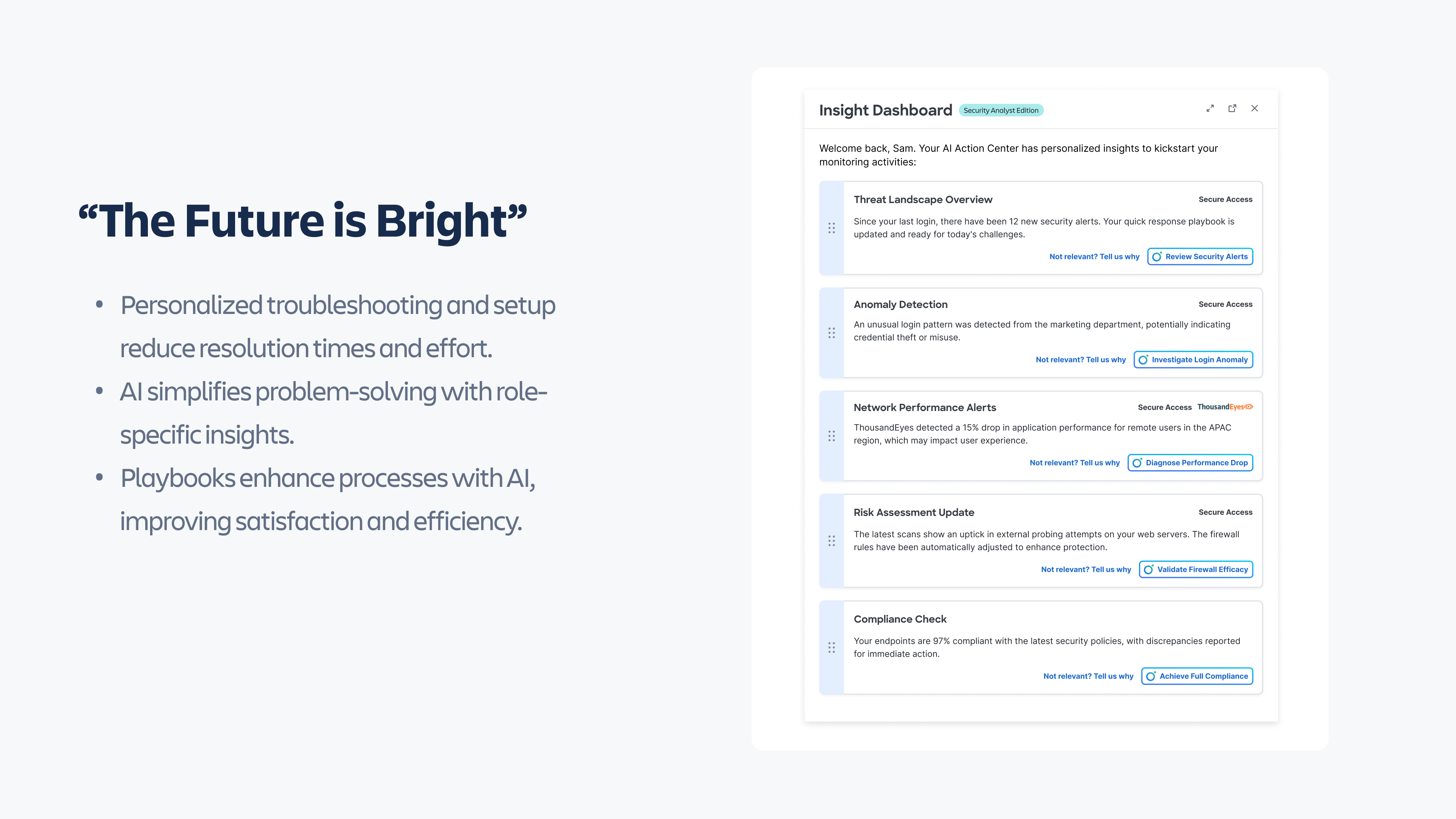
More importantly, this lays the foundation for the next evolution: an AI agent model where high-confidence, low-risk actions can be handled autonomously, with human intervention triggered only for high-stakes scenarios. Playbooks are the trust-building bridge to get there.
"The future is bright" not because AI replaces the analyst, but because it gives them back the time to focus on what truly demands their expertise.